OpenClaw: The Complete Deployment Guide for 2026
Deploy on DigitalOcean, secure your installation, connect Telegram, and discover the top 5 use cases
OpenClaw: The Complete Deployment Guide for 2026
Deploy on DigitalOcean, secure your installation, connect Telegram, and discover the top 5 use cases
OpenClaw changed everything I thought I knew about AI assistants.
With 108,000+ GitHub stars, this open-source project isn't just another chatbot. It's an autonomous agent that runs on your machine, connects to 12+ messaging platforms, and can actually do things—read files, execute scripts, control browsers, send messages on your behalf.
But most people deploy it wrong. They run it on their main machine with default settings, exposing their entire digital life to potential security risks.
This guide will show you the right way: deploying on DigitalOcean's hardened infrastructure, configuring security properly, connecting Telegram as your control interface, and leveraging the use cases that make OpenClaw transformative.
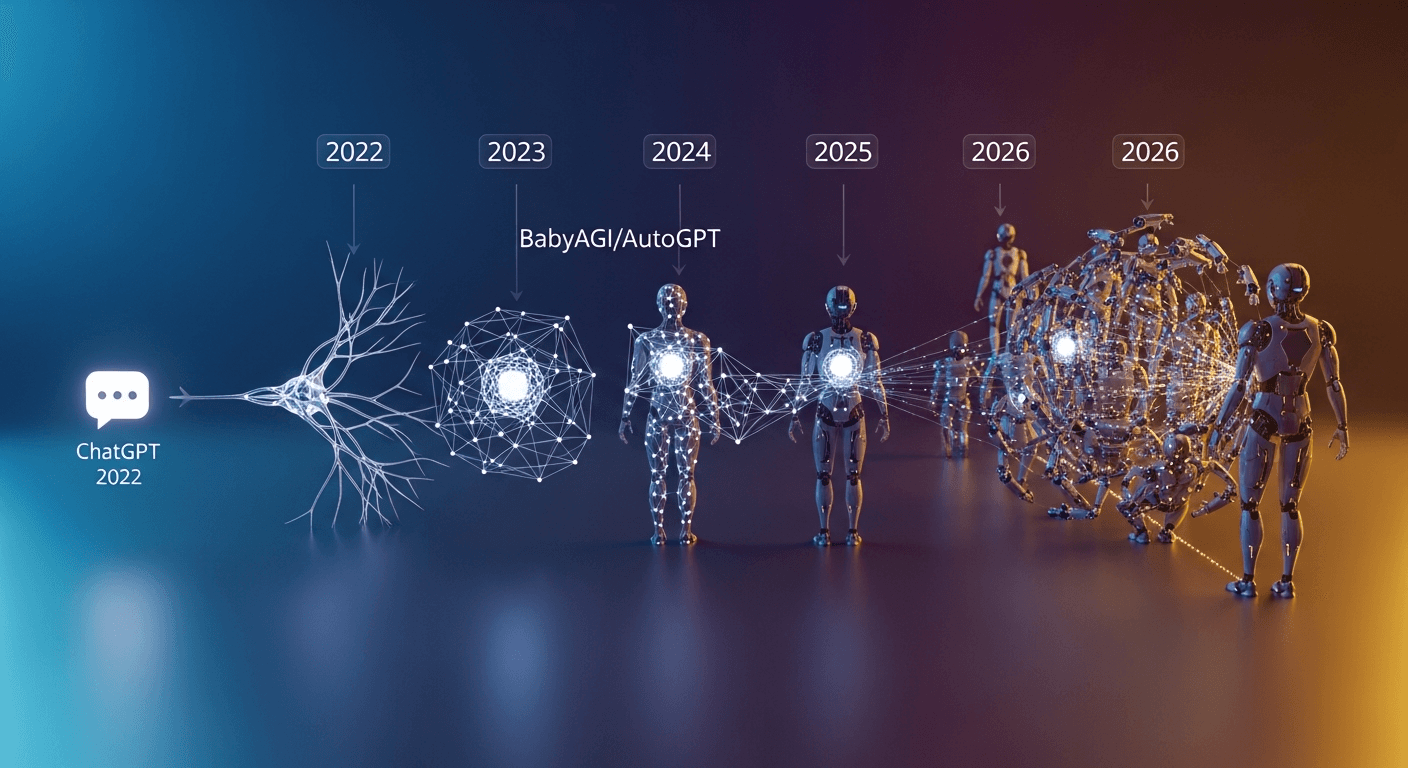
What Makes OpenClaw Different
Unlike ChatGPT or Claude.ai, OpenClaw isn't a cloud-hosted chatbot. It's a locally-running agent that operates directly on a machine you control.
This architecture provides two critical advantages:
Privacy: Your conversations and data never leave your infrastructure. There's no third-party service storing your files, emails, or messages.
Capability: Because it runs locally, OpenClaw can interact with your actual systems—reading files, executing commands, controlling browsers, sending messages through your accounts.
The project was created by Peter Steinberger (founder of PSPDFKit) and has exploded in popularity. Originally called Clawdbot, then Moltbot, it's now OpenClaw—and it's become the de facto standard for self-hosted AI agents.
Why Deploy on DigitalOcean (Not Locally)
Here's the uncomfortable truth: running OpenClaw on your personal machine means giving an AI agent access to your entire digital life. Every file. Every credential. Every browser session.
The security implications are significant. As VentureBeat noted: "Security maturity always lags behind capability. OpenClaw is in the capability explosion phase, not the hardening phase."
DigitalOcean's 1-Click Deploy solves this problem:
- Container Isolation: OpenClaw runs in Docker, isolated from the host system
- Authenticated Access: Gateway tokens are generated automatically
- Fail2ban Protection: Abusive traffic is blocked without manual configuration
- Static IP: Predictable networking for remote access
The cost is $24/month for a 4GB RAM droplet—a small price for security.
Step-by-Step: Deploying on DigitalOcean
Create Your Droplet
- Log into DigitalOcean and click "Create" → "Droplets"
- Select your nearest region for lowest latency
- Under "Choose an Image," select the Marketplace tab
- Search for "Moltbot" (the legacy name) and select it
- Choose the 4GB RAM / 2 vCPUs plan ($24/month)
- Add your SSH key and create the droplet
Wait about 3 minutes for provisioning.
Complete Initial Setup
SSH into your new server (initial setup requires root, but we'll fix this):
ssh root@YOUR_DROPLET_IP
The setup wizard starts automatically. Enter your API credentials (Anthropic API key recommended for Claude models).
Verify everything works:
openclaw doctor
Important: After initial setup, create a non-root user (see Security Hardening section) and disable root SSH login:
sudo nano /etc/ssh/sshd_config
# Set: PermitRootLogin no
sudo systemctl restart sshd
Access the Dashboard
The dashboard runs on localhost by default. Create an SSH tunnel:
ssh -L 18789:127.0.0.1:18789 root@YOUR_DROPLET_IP
Now visit http://127.0.0.1:18789 in your browser.
Security Hardening: The Non-Negotiables
OpenClaw's documentation is refreshingly honest: "There is no perfectly secure setup." But you can dramatically reduce risk with proper configuration.
Create a Non-Root User (Critical)
Never run services as root. Create a dedicated user first:
adduser openclaw
usermod -aG sudo openclaw
su - openclaw
Move the config to the new user's home directory and run OpenClaw as this user.
Configure Gateway Authentication
Edit ~/.openclaw/openclaw.json:
{
"gateway": {
"auth": {
"mode": "token",
"token": "your-32-character-random-token"
}
}
}
Generate a secure token with openssl rand -hex 32.
Important: Secure your config file permissions:
chmod 600 ~/.openclaw/openclaw.json
Enable DM Pairing Mode
This is the most important setting. Pairing mode means unknown senders receive a one-time code instead of talking to your AI:
{
"channels": {
"telegram": {
"dmPolicy": "pairing"
}
}
}
You approve legitimate users with openclaw pairing approve telegram <CODE>.
Enable Group Mention Gating
Prevent your bot from responding to every message in group chats:
{
"channels": {
"telegram": {
"groups": {
"*": { "requireMention": true }
}
}
}
}
Configure Firewall Rules
Lock down your droplet with UFW:
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw allow ssh
sudo ufw enable
The dashboard should only be accessible via SSH tunnel, never exposed directly.
Store API Keys Securely
Never commit API keys to config files tracked by git. Use environment variables:
echo 'export ANTHROPIC_API_KEY="your-key"' >> ~/.bashrc
source ~/.bashrc
Then reference in config: "apiKey": "${ANTHROPIC_API_KEY}"
Keep Your System Updated
Set up automatic security updates:
sudo apt update && sudo apt upgrade -y
sudo apt install unattended-upgrades
sudo dpkg-reconfigure -plow unattended-upgrades
Run Regular Security Audits
This should be a weekly habit:
openclaw security audit --deep --fix
The audit checks DM policies, tool access, network exposure, and file permissions—and automatically fixes common issues.
Review Tool Permissions
Check which tools have been granted dangerous capabilities:
openclaw tools list --show-permissions
Revoke unnecessary permissions with openclaw tools revoke <tool-name> <permission>.
Security Checklist Summary
Run through this checklist before going live:
- Created non-root user for running OpenClaw
- Config file permissions set to 600
- Gateway token is 32+ random characters
- DM pairing mode enabled on all channels
- Group mention gating enabled
- UFW firewall configured
- Root SSH login disabled
- API keys stored as environment variables
- Automatic security updates enabled
-
openclaw security audit --deeppasses
Connecting Telegram: Your AI Remote Control
Telegram is the ideal interface for OpenClaw. It works everywhere, supports rich formatting, and your AI can send you messages proactively.
Create Your Bot
- Open Telegram and message @BotFather
- Send
/newbot - Choose a name (e.g., "My OpenClaw Assistant")
- Choose a username ending in
bot(e.g., "MyOpenClawBot") - Copy the API token provided
Configure the Connection
Add your token to ~/.openclaw/openclaw.json:
{
"channels": {
"telegram": {
"enabled": true,
"botToken": "123456789:ABCdefGHIjklMNOpqrsTUVwxyz",
"dmPolicy": "pairing"
}
}
}
Restart the gateway:
openclaw gateway restart
Pair Your Account
- Message your bot in Telegram
- You'll receive a 6-digit pairing code
- Approve on the server:
openclaw pairing approve telegram <CODE>
Now your AI responds to your Telegram messages.
The Top 5 Use Cases
1. Email & Calendar Intelligence
OpenClaw can monitor your inbox and manage your calendar autonomously.
Example workflows:
- "When someone wants to reschedule, check my availability, update the event, and send a confirmation"
- "Every morning at 7am, send me my schedule and top priorities via Telegram"
- "Auto-archive newsletters older than 7 days"
Install the skills: npx clawdhub@latest install gmail gcal
2. Developer Workflow Automation
This is where OpenClaw shines for technical users. Developers are refactoring PRs and deploying code—all from Telegram while away from their computers.
Example workflows:
- "Review the latest PR and suggest improvements"
- "Build and publish my CLI tool to npm"
- "Monitor server logs and alert me if errors exceed threshold"
Install the skills: npx clawdhub@latest install github npm docker
3. Daily Briefings & Task Management
Configure OpenClaw to prepare morning summaries delivered through your preferred messaging platform.
What you get:
- Weather for your location
- Today's calendar events
- Top priorities from your task manager
- Key metrics from your dashboards
Configure via cron jobs in your config file.
4. Browser Automation & Research
OpenClaw can fill forms, extract data, and research topics using browser control.
Example workflows:
- "Research this person before my meeting and summarize their background"
- "Fill out this expense report with last month's receipts"
- "Find the best price for this item across 5 retailers"
Security warning: Browser control grants access to all logged-in sessions. Mitigate risk by:
- Using a dedicated browser profile with no saved passwords
- Never logging into banking/sensitive sites in the automated browser
- Running browser automation in a separate container if possible
- Reviewing browser action logs regularly:
openclaw logs browser --tail 100
5. Smart Home & IoT Control
Control your connected devices through natural conversation.
Example workflows:
- "Turn off all lights when I say 'goodnight'"
- "Set thermostat to 72 when I leave work"
- "Alert me if garage door is open after 10pm"
Install the skills: npx clawdhub@latest install homeassistant homekit
The Skills Ecosystem
OpenClaw's power comes from its extensibility. The community maintains 700+ skills across 28 categories:
- DevOps & Cloud (41 skills): Azure, Kubernetes, Vercel, Docker
- AI & LLMs (38 skills): Model integration and optimization
- Notes & PKM (44 skills): Notion, Obsidian, Roam
- Productivity (41 skills): Task managers, time tracking
- Marketing (42 skills): GA4, Google Ads, HubSpot
- Smart Home (31 skills): Home Assistant, HomeKit, Alexa
- Finance (29 skills): Banking, crypto, budgeting
Install any skill with:
npx clawdhub@latest install <skill-name>
Monitoring & Backups
Enable Action Logging
Track everything your AI does:
openclaw config set logging.level verbose
openclaw config set logging.actions true
Review logs regularly:
openclaw logs --since 24h | grep -E "(EXECUTE|SEND|DELETE)"
Set Up Backups
Back up your configuration and conversation history:
# Weekly backup script
tar -czf ~/openclaw-backup-$(date +%Y%m%d).tar.gz ~/.openclaw/
Consider DigitalOcean's automatic backup feature ($4.80/month).
Set Up Alerts
Configure Telegram alerts for suspicious activity:
{
"alerts": {
"enabled": true,
"channel": "telegram",
"triggers": ["failed_auth", "new_pairing", "dangerous_tool_use"]
}
}
What's Next
OpenClaw represents a fundamental shift from asking AI questions to delegating AI actions. The capabilities will only expand as the community builds more skills and the core team hardens security.
Start with DigitalOcean's 1-Click Deploy. Configure security properly from day one. Connect Telegram as your command interface. Then gradually explore the use cases that matter to you.
The future of personal AI isn't chatting—it's delegation.
Resources:
Written by
Global Builders Club
Global Builders Club
If you found this content valuable, consider donating with crypto.
Suggested Donation: $5-15
Donation Wallet:
0xEc8d88...6EBdF8Accepts:
Supported Chains:
Your support helps Global Builders Club continue creating valuable content and events for the community.